Introduction
In today’s fast-evolving digital landscape, the push towards automation is more than just a trend. It’s a fundamental shift in how businesses operate across sectors. From streamlining operations in marketing and sales to enhancing efficiencies in IT and HR processes, automation has become a cornerstone of modern business strategies. However, this transformation brings with it a critical challenge that cannot be overlooked: cybersecurity in the age of automation. As we delve deeper into the era of automated workflows and AI-driven solutions, the importance of cybersecurity measures becomes increasingly paramount.
The concept of cybersecurity in the age of automation is not just about protecting data in a traditional sense. It’s also about creating a resilient environment where automated systems can thrive, free from the threats of cyber attacks that evolve as quickly as the technologies they aim to compromise. This integration of cybersecurity and automation presents a unique set of challenges and opportunities for businesses. On one hand, automated systems can become targets for sophisticated cyber threats, from ransomware attacks disrupting entire operational flows to phishing scams that leverage automated communications. On the other hand, the very technologies driving automation offer new avenues for defending against these threats. This showcases the dual-edged nature of cybersecurity in the age of automation.
Exploring Cybersecurity in the Age of Automation
As we embark on this exploration of cybersecurity in the age of automation, it’s crucial to understand that this is not merely a technical issue but a strategic necessity. The balance between leveraging the benefits of automation and ensuring the security of these systems is delicate. Businesses must not only anticipate and mitigate potential cyber threats but also cultivate a culture of cybersecurity awareness that evolves alongside their automated processes. This blog post aims to shed light on the complexities of cybersecurity in the age of automation, offering insights into the challenges, strategies, and tools that can help businesses navigate this new terrain confidently and securely.
The Evolving Landscape of Cyber Threats in Automated Systems
As we navigate through the age of automation, the cybersecurity landscape continues to evolve at an unprecedented pace. The integration of automated systems in business operations has not only streamlined processes but also opened new avenues for cyber threats. Understanding these threats and the systems they target is the first step in fortifying our defences in the realm of cybersecurity in the age of automation.
Understanding Automated Systems
At the heart of the digital transformation lies automation—technology designed to perform tasks with minimal human intervention. From automated marketing campaigns that engage customers through personalized emails to HR systems that manage employee data and facilitate onboarding processes, automation permeates every aspect of modern business. However, the efficiency and scalability offered by these automated systems also make them attractive targets for cyber attacks. Recognizing the critical role of cybersecurity in the age of automation is essential in protecting these automated processes from potential breaches.
The Cyber Threat Spectrum
The spectrum of cyber threats is broad and constantly evolving. Automated systems, with their reliance on data and networked operations, are particularly vulnerable to a range of cyber attacks:
- Ransomware attacks can cripple automated workflows, locking out essential data and demanding hefty ransoms for its release. These attacks not only disrupt operations but also pose a significant threat to data integrity and privacy.
- Phishing scams, increasingly sophisticated and automated, exploit human error to gain unauthorized access to systems. Automated emails and messages, designed to mimic legitimate communications, can lead to significant breaches if not intercepted.
- DDoS (Distributed Denial of Service) attacks target the very foundation of automated systems—their networked infrastructure—overwhelming servers with a flood of requests and disrupting services.
The adaptability of cyber threats underscores the need for equally dynamic cybersecurity measures in the age of automation. Understanding these threats is the first step in developing robust defence mechanisms.
The journey towards cybersecurity in the age of automation is complex, filled with evolving threats and innovative defence strategies. As businesses increasingly rely on automated systems to drive operations, the integration of comprehensive cybersecurity measures becomes non-negotiable. The next section will explore the strategies and technologies pivotal in defending against the cyber threat spectrum. It’ll highlight the critical role of cybersecurity in safeguarding the future of automation.
Omnitas Newsletter
Sign up for our monthly newsletter to stay up-to-date on our latest blog articles, videos and events!
Thank you!
You have successfully joined our subscriber list.
Cybersecurity Strategies for Automated Systems
In the dynamic interplay of automation and cybersecurity, devising robust strategies is paramount for safeguarding automated systems. Automation demands a cybersecurity framework that is both resilient and adaptable, capable of defending against both current and emerging threats. Here, we explore the pivotal strategies and technologies that form the cornerstone of cybersecurity in the age of automation.
The Role of AI and Machine Learning in Cybersecurity
In the forefront of defending the digital frontier, Artificial Intelligence (AI) and Machine Learning (ML) stand as beacons of hope. Their role in cybersecurity cannot be overstated:
- Predictive Analysis: AI and ML algorithms excel at identifying patterns in data. In turn, this enables them to predict and identify potential cyber threats before they materialize.
- Automated Response: In the event of a detected threat, AI-driven systems can initiate automated responses. This mitigates risks in real-time and often without the need for human intervention.
- Continuous Learning: Perhaps most crucially, AI and ML systems learn from every interaction, continuously improving their ability to detect and respond to threats. This learning capability is vital for keeping pace with the rapidly evolving landscape of cyber threats.
While AI and ML offer significant advantages, they are not without limitations. The sophistication of cyber threats means that these technologies must be part of a broader, multi-layered approach to cybersecurity.
Essential Cybersecurity Practices for Automation
Beyond the cutting-edge capabilities of AI and ML, several foundational practices remain critical for the cybersecurity of automated systems:
- Regular Software Updates and Patch Management: Automated systems must be kept up-to-date with the latest software patches and updates. These are often designed to address known vulnerabilities, making regular updates a simple yet effective defence mechanism.
- Strong Access Controls and Authentication Methods: Implementing stringent access controls and multi-factor authentication can significantly reduce the risk of unauthorized access to automated systems.
- Cybersecurity Training for Employees: Human error remains a significant vulnerability, even in automated systems. Regular training on cybersecurity best practices can empower employees to recognize and avoid potential threats.
The integration of AI and ML technologies with foundational cybersecurity practices offers a robust defence against the threats posed in the age of automation. However, these strategies require continuous evaluation and adaptation to remain effective.
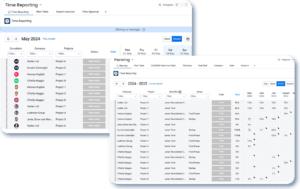
monday.com and Make: Bolstering Cybersecurity in Automation
The selection of tools and platforms can significantly impact the cybersecurity posture of a business. Two standout examples of platforms that integrate seamlessly with automated systems while prioritizing security are monday.com and Make. Both platforms offer unique features that not only enhance automation but also incorporate strong cybersecurity measures. This further showcases the symbiotic relationship between automation and cybersecurity.
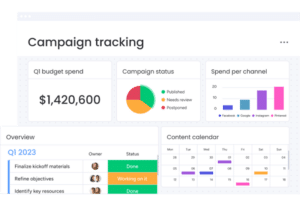
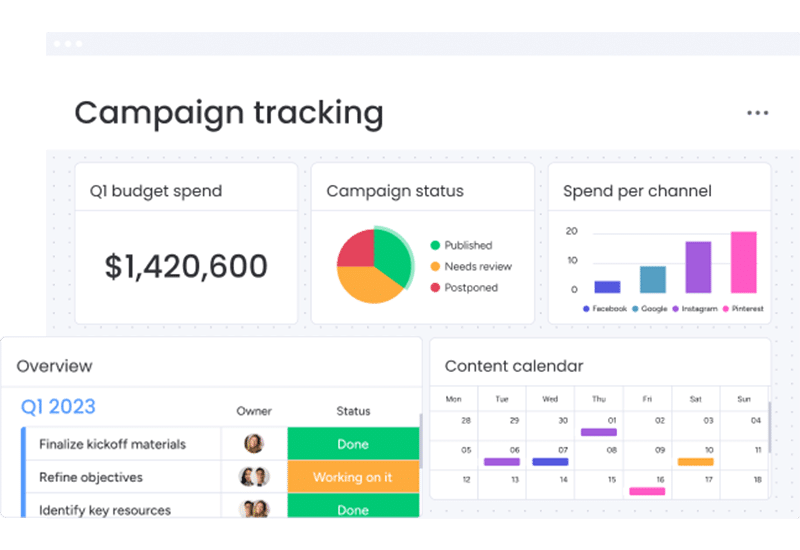
monday.com: Enhancing Team Collaboration Securely
monday.com, a leading project management tool, is renowned for its ability to streamline collaboration and automate workflows. In the context of cybersecurity in the age of automation, it goes beyond mere efficiency:
- Encrypted Data: monday.com ensures that all data, both at rest and in transit, is encrypted. This layer of security protects sensitive information from unauthorized access, a cornerstone of cybersecurity in the age of automation.
- Two-Factor Authentication (2FA): By implementing 2FA, monday.com adds an extra layer of security to the login process. As a result, this significantly reduces the risk of unauthorized access.
- Compliance and Certifications: Adhering to international cybersecurity standards, monday.com maintains several certifications. These include ISO/IEC 27001 and GDPR compliance, ensuring that cybersecurity in the age of automation is not just a goal but a reality.
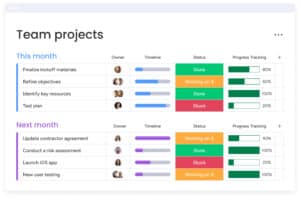
Make: Secure Automation Workflows
Make offers a powerful platform for creating complex, automated workflows with ease. Its commitment to cybersecurity is evident in several features:
- Data Privacy and Security: Make ensures high standards of data privacy and security, including compliance with GDPR, to protect user data from cyber threats.
- Customizable Permissions: Users can set granular permissions for different parts of their automated workflows. This ensures that only authorized personnel have access to sensitive operations, a key practice in cybersecurity in the age of automation.
- Secure Connections: Make uses secure connections for all data transfers, employing encryption to safeguard data integrity and confidentiality during automation processes.
monday.com and Make exemplify how automation platforms can and should integrate robust cybersecurity measures. Their features enhance the efficiency and functionality of automated systems and ensure these systems are secure from cyber threats. This dual focus is crucial for businesses aiming to leverage the benefits of automation while maintaining a strong cybersecurity posture in the age of automation.
The integration of platforms like monday.com and Make into a business’s automation strategy signifies a step forward in addressing the complex challenges of cybersecurity in the age of automation. By choosing tools that prioritize security as much as efficiency, businesses can navigate the digital landscape with confidence. As a result, this ensures their automated processes are both powerful and protected.
Conclusion
As we’ve journeyed through the intricacies of cybersecurity in the age of automation, it’s become clear that the fusion of automation and cybersecurity is not just a trend, but a necessity for modern businesses. The evolution of cyber threats alongside automated systems presents a complex challenge, yet also an opportunity to fortify and innovate within our digital defences. The roles of platforms like monday.com and Make have been highlighted as exemplary in integrating robust cybersecurity measures with automation, offering businesses the tools to navigate this landscape with confidence.
The adoption of such platforms is a critical step towards ensuring that your automated processes are not only efficient and streamlined but also secure from the myriad of cyber threats that pervade the digital age. It’s a testament to the fact that in the age of automation, cybersecurity is not just a technical requirement but a strategic imperative.
Take Action Now
In the spirit of proactive cybersecurity and efficient automation, we invite you to explore monday.com and Make through our exclusive free trial links. These platforms have been pivotal for businesses seeking to enhance their automated workflows without compromising on security. Whether you’re looking to automate marketing campaigns, streamline project management, or secure data transfers, monday.com and Make offers the solutions you need to do so securely and efficiently.
And remember, implementing these tools effectively requires expertise and strategic insight. At Omnitas, we specialize in leveraging the power of platforms like monday.com and Make to not only enhance your business operations but to ensure they’re secure, compliant, and optimized for success. If you’re considering integrating these tools into your business or looking to maximize their potential, do not hesitate to reach out to us below. As experts in both, we’re here to guide you through every step of the process, ensuring your transition to automated systems is seamless, secure, and successful.
If you found this blog post useful, make sure to sign up for our monthly newsletter below. Stay in the loop regarding all things business efficiency and automation!